All you need to know about SASE
Corporate environments gain more prominence as their brands are positioned in the online environment. This adds value to companies and equips them to increase sales conversion.
As a result, cyber attacks become increasingly frequent and can take place for different purposes – either to jeopardize a company’s operations or to hijack data and demand ransom. This is where SASE cybersecurity solutions come in to prevent these types of threats in enterprises.
Learn what it is and the advantages of implementing this service.
What is SASE?
SASE stands for Secure Access Service Edge, initially proposed by Gartner in 2019 to describe a modern cybersecurity architecture aimed at converging environment protection and analysis services for cybersecurity aspects. Combining a variety of features with security functions. Its goal is to create a network infrastructure with the direct application of cybersecurity, protecting and preventing threats and cyber attacks on the network, servers, and equipment connected to the internet.
To do so, a SASE solution is adaptable to the risk analyzed in a given environment, allowing strategies to be created to prevent the network and mitigate the risk of attacks.
How is the SASE network structure arranged?
SASE uses several integrated hardware and software features to create a more secure network structure. In a nutshell, it is structured by:
- Routing processes;
- Next-generation firewall;
- Monitoring systems;
- Network traffic analysis and contextualization;
- Protocol application and behavior.
Every security information is provided, sent, and managed directly in the cloud. The SASE provider performs critical functions, such as:
- Secure Web Gateway (SWG): a cybersecurity solution provided on the network between internet users and the network, creating a barrier to malicious traffic.
- CASB: an access security agent that prevents cyberattack and attacker access directly in the cloud. Data is preserved by blocking the intrusion;
- Zero Trust: a network security service that prevents anyone from accessing a device that is not authenticated. This verification is performed by IT to allow access on the network;
- Domain Name System: management of computer names connected to the network. It allows you to map your network and keep track of addressing information, IP access, and server names;
- Date Loss Prevention (DLP): this security feature ensures that confidential information is not accessed illegally. In addition, it prevents data hacking, theft, and misuse;
- FWaaS: firewall-as-a-service for network protection that prevents unauthorized access by intruders to your computer or network;
- Browser isolation: it prevents malicious sites from attacking your network through your browser and allows safer access for users accessing your Internet pages.
All of the above features are offered directly in the cloud and ensure secure web browsing and access to the user, be it via computers or mobile devices.
What are the main advantages?
By applying the SASE architecture, the risks of attacks are reduced through cybersecurity that takes place in the cloud. In fact, SASE offers a great deal of advantages in terms of network security, as it prevents malware, performs a web filtering process, promotes protection against theft of important information, and provides firewall policies to protect customers and sensitive data.
Other strong points are highlighted below. Learn more about them:
- Reducing costs and complexity;
- Protecting users’ continuous access;
- Enabling more secure remote and mobile access;
- Improving security by applying a reliable policy.
As you can see, SASE provides security to websites, applications, and APIs by blocking the action of malicious agents through secure end-to-end access. This gives your company a competitive advantage, as it makes your systems reliable and ensures the preservation of your customer’s personal data, generating concept and authority for your company.
How to implement SASE in practical terms?
Having questions about implementing security services is commonplace. What needs to change after all? What are the most appropriate features? Look no further: read below our real-world step-by-step to deploy SASE.
The initial actions in implementing SASE in your company includes learning your business network infrastructure and identifying the actual needs and demands. This is important, because as it is an adaptable resource for each type of business, understanding the company’s scenario is key to define which features and capabilities are essential for the cybersecurity of your network.
In practice, the following steps must be taken to deploy SASE:
-
- Assess the business landscape and your network infrastructure;
- Identify the ideal features for your circumstances;
- Consider recent threats to determine which environment should be given priority;
- Assess network demands and gaps;
- Identify existing and lacking network protection features.
Let’s now address some of the challenges posed by SASE technology to enterprises. Most significantly, it requires adapting the business culture so cybersecurity procedures can work. In addition, these are practices that need to be conducted by qualified professionals with expertise in network protection and infrastructure.
As cyber attacks become increasingly frequent, investing in secure networks is a must in the corporate world. You need to promote an SASE-driven business culture and be assured that your company’s and your customers’ data and information are secure. When looking at SASE solutions, it is important to examine the available features, the flexibility to adapt to your specific scenario, and also the technical support. Below are some of the features of a good SASE framework:
- DDoS attack protection;
- BGP advertisement monitoring;
- Extended Detection and Response (XDR);
- IP block management;
- Rule profiles for IP blocks;
- Web Application Firewall
- Possible integration via API.
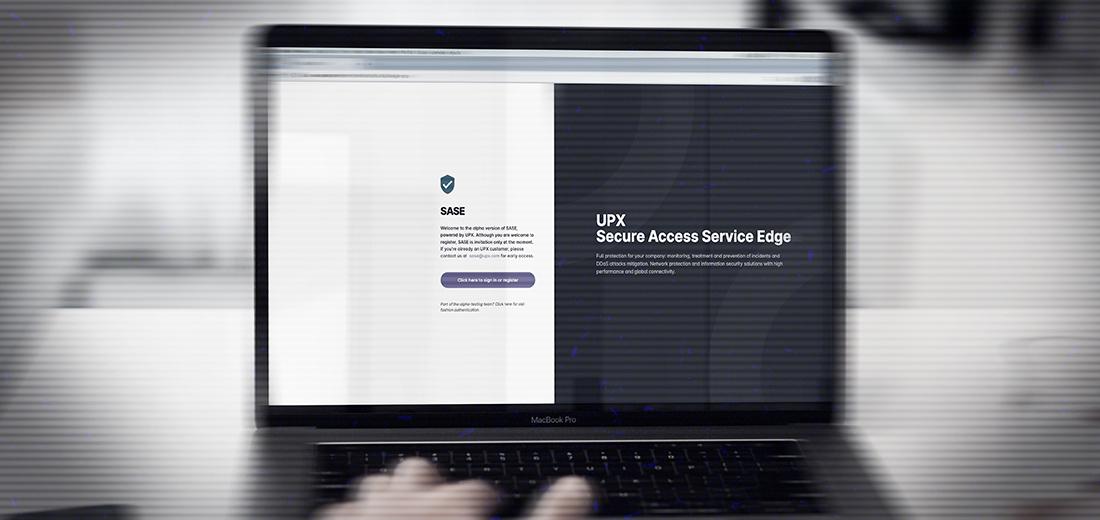
At UPX, we have a SASE solution that integrates all these features and more. Contact us for
more information.
Get in touch with UPX
Send your contact so that one of our specialists can get back to you.


